Tech
-
6 October, 2022
Digital Asset Recovery process has use cases far beyond simple theft
The Digital Asset Recovery Toolset would mean that anybody with a court order establishing ownership of digital assets can use...
-
6 October, 2022
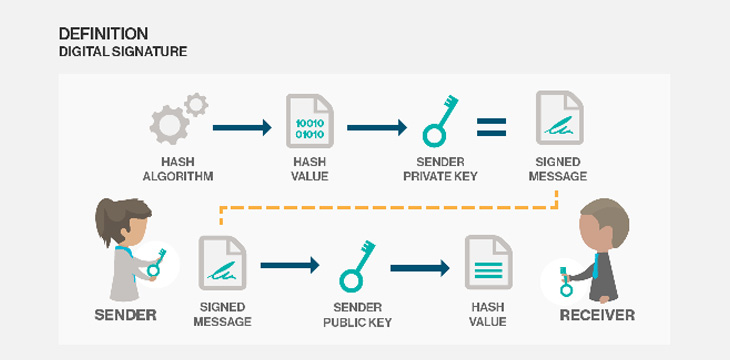
Digital signatures
A digital signature still requires an identity, and for high-end and high-value transactions, identity can be provided through certificate authorities...
-
5 October, 2022
Asset seizure was possible in original Bitcoin
Today, many in the digital currency space believe asset seizure and freezing to be technically impossible, as the system is...
-
5 October, 2022
Interested in Zero-Knowledge Proofs on BSV? Join the BSV sCrypt Zero-Knowledge Proof Hackathon!
The hackathon is open to all developers interested in ZKPs and cryptography, whether they're active in the BSV or blockchain...
-
4 October, 2022
Why put chat on-chain?
Upon the re-launch of Bitchat, naturally questions arose of why store chat messages on a blockchain. Especially if the chat...
-
4 October, 2022
Russia to allow block reward mining, but only in energy-rich regions
A new bill set to be tabled in parliament will relegate BTC mining to regions with hydroelectric and nuclear power...
-
4 October, 2022
Efficient zk-SNARKs on Bitcoin: Technical explainer
After all the optimizations, sCrypt was able to cut the Script size of pairing by 100X to 5MB, and they...
-
1 October, 2022
China’s Gansu province warns against BTC mining in national data centers
The province has been cracking down on block reward miners for the past year and issued the warning amid mega...
-
30 September, 2022
Chinese university renames engineering department after metaverse, sets up new major
In an attempt to put China at the forefront of tech development, a local university opens a course focusing on...
-
27 September, 2022
Blockchain Innovation Program launches to promote Bitcoin development
The course, developed by the Bitcoin Association for BSV, dives into hash functions, Merkle trees, digital signatures, and more over...
-
26 September, 2022
Zero-Knowledge private machine learning on Bitcoin
The application of Zero-Knowledge Proof machine learning on Bitcoin's neural networks allows sensitive data to be kept private while its...
-
22 September, 2022
Introducing zkBattleship: The world’s first interactive Zero-Knowledge Proof tutorial
sCrypt is excited to introduce zkBattleship, the world’s first and only interactive ZKP tutorial, aimed at developers who want to...
Recent
Trending
Most Views

 09-21-2024
09-21-2024