Tech
-
11 January, 2022
Kosovo bans digital currency mining after winter blackouts
Kosovo is eliminating all non-essential energy needs, such as block reward mining, after winter-fueled blackouts led the nation to a...
-
11 January, 2022
Deadly protests in Kazakhstan lead to 5-day Internet outage, BTC hash rate drops 13%
Kazakhstan has been experiencing its deadliest protests ever with over 160 dead, and BTC hash rate took a nosedive after...
-
8 January, 2022
Trustless outsourced vanity address generation
To overcome the drawback of the previous Zero-knowledge key-statement proof, sCrypt conducted the exchange entirely on chain using a smart...
-
2 January, 2022
ECDSA signature verification in Script
sCrypt has implemented ECDSA signature verification algorithm in Script to verify if an arbitrary message is signed by a private...
-
2 January, 2022
Hackers use ‘Spider-Man: No Way Home’ to spread Monero mining malware
The latest Spider-Man film is proving quite popular, and hackers are taking advantage to spread a very well-disguised mining malware...
-
1 January, 2022
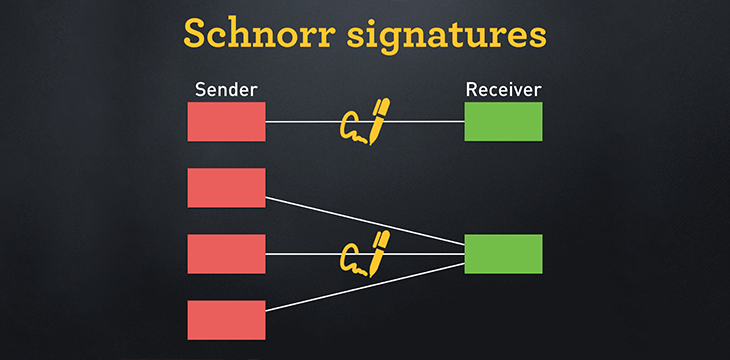
Schnorr signatures on Bitcoin
In this article, sCrypt shows how to implement Schnorr Signatures using the original Bitcoin Protocol. Schnorr is an alternative algorithm...
-
31 December, 2021
The biggest digital currency hacks in 2021
"Bring down the banks" has become a mantra in some corners of the industry, but what few talk about is...
-
30 December, 2021
Iran cuts off power to miners to save energy for winter
The Iranian national grid operator said that this is one of many measures meant to ensure that residents won’t experience...
-
28 December, 2021
Get your ‘Introduction to Bitcoin Infrastructure’ with Bitcoin SV Academy new course
In this course, learners will get a basic understanding of the role of nodes and node operators, as well as...
-
28 December, 2021
Tencent, Huawei, and Alibaba lead 1,300+ Chinese companies in metaverse trademark race
The money is flowing into the metaverse, with the emerging sector receiving over $1.5 billion, most of it in the...
-
27 December, 2021
Introducing Learn sCrypt
Learn sCrypt is a series of lessons that split the development of an on-chain game Tic-tac-toe on the Bitcoin network...
-
26 December, 2021
Access blockchain data from Bitcoin smart contracts: Part 5
sCrypt's Xiaohui Liu demonstrated how to implement relative locktime in Bitcoin without a new opcode in part 5 of accessing...
Recent
Trending
Most Views

 09-22-2024
09-22-2024